Checkpoint Endpoint Security Failed To Topology
The correct number is up to 10. - Endpoint Security Management Endpoint Security Server Upgrades 01162444 After you upgrade an Endpoint Security Server to E80.50, you must install all policies before you upgrade Endpoint Security clients. - 01203454 Policies 35, 36, and 37 are used by the Full Disk Encryption blade and were previously used by Media Encryption & Port Protection. If a client upgrades to this version without Full Disk Encryption, and previously had Full Disk Encryption, or Media Encryption & Port Protection, these policies are not deleted. These policies try to sync with the Endpoint Security Server, but fail to do so. This leads to repeated attempts to synchronize. - Initial Security Analysis Client 01119962 The link to download the Endpoint Security Initial Client from the Compliance Analysis Report does not work on Windows 64-bit computers.
- Checkpoint Endpoint Management
- Checkpoint Endpoint Security Failed To Download Topology
- Cannot Uninstall Checkpoint Endpoint Security
For configuration specific to Endpoint Security VPN. On the Topology page. In Policy > Global Properties > Remote Access > VPN — Basic.
- 01488103, 01511203, 01511647, 01535408, 01555564, 01560056 IPS protection 'TCP Off-Path Sequence Inference' drops TCP packets originated by Security Gateway. - 01367531, 01375276, 01375404, 01375414, 01375713, 01375715, 01375716, 01380512, 01511033 IPS protection 'TCP Off-Path Sequence Inference' drops TCP 'RST' packets with 'ACK' value 0.
With a customizable management dashboard, administrators have maximum visibility into the specific security areas important to the organization. They can take the steps to deploy and remediate endpoints to ensure compliance with company policy. The forensics capability within SandBlast Agent provides security teams with a deeper understanding of security events by providing a comprehensive view of the full attack lifecycle, collecting actionable data on events, and accelerating remediation to limit any damages.
We support upgrade from VPN Clients to the Endpoint Security Clients. This allows existing Remote Access Clients to add additional Security Blades. • Endpoint Security Client for Mac OS X: Including Firewall for desktop security, Compliance, Full Disk Encryption, and Remote Access VPN for transparent remote access to corporate resources. We support upgrade from Endpoint Security VPN to the Endpoint Security Clients. This allows existing Endpoint Security VPN users to add additional Security Blades. What's New in Endpoint Security Clients Endpoint Security E80.50 Client for Windows • Media Encryption & Port Protection • Support for unauthorized and authorized file type scan configuration. • Full support for classifying data, which is written to a removable device, as business data or non-business data.
What is EndPoint Connect? Check Point`s Endpoint Connect software provides a number of client side security based features such as Anti-virus/Anti-spyware. Firewall/Email Protection, Program Control and Remote Access VPN.
On the R70 Security Management server, edit the file: /opt/CPNGXCMP-R70/lib/vpn_table.def 2. Scroll down to the section that starts with: /* Slim Client gateway tables */ 3. Add the entry for the ccc_sessions table below it: ccc_sessions = dynamic expires 900 keep sync kbuf 1; 4. After adding this entry to the vpn_table.def file, open SmartDashboard and re-install policy to the NGX R65 Security Gateway(s). Further details can be found within the Check Point KB article sk43124 Licensing Details on licensing can be found within Check Points KB article sk43329.
Media Encryption Offline Access Tool E80.50 for Mac For more information on Check Point Endpoint Security releases, see: and. For more information, refer to. You can also visit our, or to ask questions and get answers from technical peers and Support experts. Endpoint Security Clients E80.50 Endpoint Security Clients are managed by SmartEndpoint on an R77 Security Management Server (see ).
- 01201453 If the policy defines the minimum percentage of media used for encrypted storage to be 100%, encrypting a removable device that is formatted as NTFS might fail. This setting is in the properties of ' Allow offline access to encrypted storage devices'. - 01181767 If the policy is ' Encrypt Business Data' and the ' Word' category is selected as a business files category, if you copy a ZIP file to the non-business drive, you are asked to encrypt the file.
• When configuring a rule, VSX Gateway itself does not appear in the ' Next Hop Gateway' list (only other Virtual Systems / Virtual Routers appear). - 01918066 PPTP traffic does not pass through Virtual System with enabled CoreXL and Hide NAT. - SecureXL 00264417 If either of these features/settings is already enabled: • Multi-Queue on one of the non-SAM interface, or • Hyper-Threading in BIOS and you then enable or disable SAM mode on one of the interfaces then: • Reboot the system. • Log in to Expert mode. • Re-configure the Multi-Queue by running this command: [Expert@HostName]# cpmq reconfigure • Reboot the system again. Refer to from.
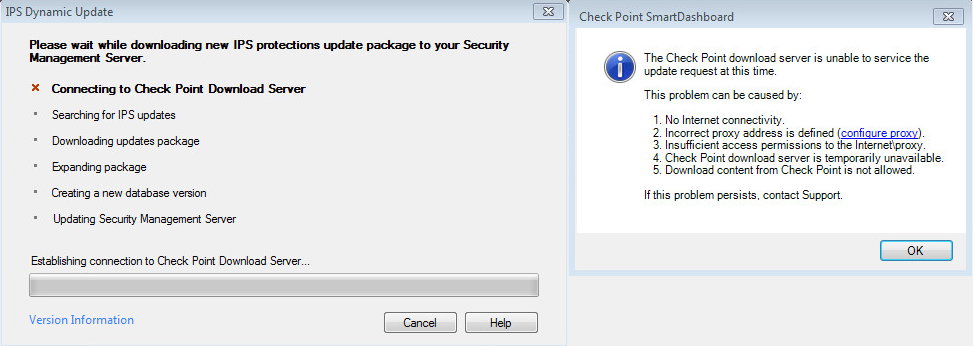
Spl drumxchanger mac crack. Hello all, i am using a Checkpoint R6 HFA_70 Cluster with a lot of VPN Clients. The most of them are Secure-Client-Users, which works fine. I am trying to have a coexistence with Endpoint Connect because i have 2 Users with Windows 7 / 64 Bit. I created a Client like described in the manual and updated the connectra plugin on smartcenter and both firewall-boxes. After that i installed the policy. SecureClient still works fine. Endpoint Connect terminates with 'Failed to download Topology' Message.
Checkpoint Endpoint Management
For example, two default routes with different Gateway IP addresses. - 01215129 After successfully configuring interfaces, static routes, DNS, NTP and Proxy settings on the Security Gateway, Audit logs are sent to the Security Management Server: • Audit logs are sent only after a first policy install • Central Device Management actions (such as ' Push Settings To Device' and ' Run. Script') do not generate an Audit log - 01215133 The Central Device Management ' Open Shell' feature (click on ' Actions' - go to ' Maintenance' menu) does not work with Gaia Security Gateways that have an IPv6 address configured. - Gaia Automatic Software Updates - If Mobile Access blade is enabled or active on Security Gateway, then after upgrading to R77, the message ' Installed, self-test failed' might appear for the R77 package.
- 01400416, 01426321, 01427424, 01441931, 01442358 Traffic over VPN tunnel does not pass for several seconds during policy installation on Security Gateway (which causes traffic loss). - 01424048, 01424181, 01466269 Memory leak in VPN code.
- 01215113 The ' Get Topology' button is no longer available in Security Gateway's ' Topology' page. To fetch interfaces and topology: • Go to the 'Firewall' tab. • In the left upper pane, go to the 'Gateways' view. • Select on a Gaia Gateway. • In the top tool bar, click on ' Actions' - go to ' Maintenance' menu - click on ' Fetch Settings From Device'. Interfaces cannot be added or deleted via the Security Gateway's ' Topology' page.
- 00927816 Upgrading an Endpoint Security Client from E80.10 on a Windows 7 32-bit computer is not supported, if one or more of these blades is installed: • Media Encryption and Port Protection • Full Disk Encryption • WebCheck - 01353748, 01248909, 01353748 Cannot install policy when using devices groups in peripheral device access configuration. Refer to - Endpoint Security Client Upgrades 01160298 Upgrade from ZoneAlarm Extreme Security version 11.0.000.504 to Endpoint Security Client is not supported.
(Please remember to honor your company's IT policies before installing new software!) • • • •.
Workaround: Allow all applications. - Push Operations 01142237 If you push operations to a device and then Reset the device, you might get this error: Another administrator has changed an object that you are trying to change. Discard the changes, refresh the data, and Reset the device again. - 01193324 It is not recommended to push a Push Operation to more than 400 users in one operation.
Workaround: First copy the files to the local computer and then copy them to the encrypted container. - 01189778 In some situations, when a user clicks on ' Remove Encryption' in the client UI, it does not work. If the user inserts the device again and then clicks on ' Remove Encryption', the encryption is removed successfully.
To resolve this run through the following steps: 1. On the R70 Security Management server, edit the file: /opt/CPNGXCMP-R70/lib/vpn_table.def 2.
Checkpoint Endpoint Security Failed To Download Topology
Users are targets of phishing emails that may contain links to websites infected with this malware. To prevent these new and emerging threats, IT departments need comprehensive security even on endpoint devices no matter where they go.
- 01319816, 01320627, 01320628 Memory leak in CPD when working with Anti-Malware statistics. - 01361489, 01364092, 01365030, 01367220, 01369323, 01369833, 01371645 ' Check Point Online Web Service failure. Refer to for more information.' Log appears repeatedly in SmartView Tracker when Anti-Virus or Anti-Bot or both are enabled. - Application Control 00781189 Dynamic Objects are not supported in Application Control rulebase.
• Can be installed onto Windows 7 64-bit. Disadvantages • An additional SNX (SSL Network Extender License) is required due to that in which it authenticates across HTTPS (vistor mode) • Link Selection is disabled (this is due to sites being defined via a single IP address). • MEP configurations can only be achieved by using Geo-Cluster DNS name resolution. Installation on an R65 Gateway Upgrading a R65 Gateway to R65 Endpoint Connect: • Ensure that you are running HFA40 or higher.
Endpoint Connect terminates with 'Failed to download Topology' Message. Any ideas how to solve this? Regards bytesleuth.
Port 443/tcp is not listening due to no SNX (SSL Network Extender) License being present. Issue: Failed to download topology Endpoint Connect fails to connect to NGX R65 Security Gateways that are managed by an R70 Security Management server with error: 'failed to download topology'. To resolve this run through the following steps: 1.
- 01368631, 01371531, 01427548 Resource field shows ' *** Confidential ***' in Application Control / DLP logs on 3rd party LEA OPSEC client when using Permissions Profile. 01493176, 01493994 Changes in Administrator password and allowed GUI clients are not synchronized in Management HA deployment. - 02019438, 02019725 fwm process memory leak and crash after renaming many objects in a large database. - Multi-Domain Security Management 01290396, 01292842, 01292845, 01295784 MDS HA status is switched to ' Lagging' every 6 hours.
Configuration To enable Endpoint Connect configure/enable the following settings: Under the Check Point Gateway Object 1. Enable VPN 2.
SecureClient still works fine. Endpoint Connect terminates with 'Failed to download Topology' Message. Any ideas how to solve this? Regards bytesleuth.
- VSX - SAM Block rules are not supported in VSX mode. - 01143713 Up to 128 interfaces are allowed for each Virtual System. - 00892773 VTI interfaces are not supported in VSX mode. - 01159014 IPv6 VPN connections are not supported on a VSX Gateway. - 01453316 Check Point VSX OID Branch 1.3.6.1.4.1.2620.1.16 can not be queried per Virtual System.
Cannot Uninstall Checkpoint Endpoint Security
• In non-DMI configuration: • The SNMP query should be sent to the physical IP address of the external interface on the VSX machine. - 01181667 IPS Packet Capture does not work on a Virtual System created on a Domain Management Server that is not Main Domain Management Server (where the object of VSX Gateway / VSX cluster was created). A ' Connection failed' error shows in the SmartView Tracker IPS log when clicking on View Packet Capture in a log generated by a Virtual System.
- 00527267 Performance Pack (SecureXL) Heavy Load Quality of Service feature (HLQoS) is not supported. - 00575640 Cloning and Templates are not supported for vSEC Gateway for ESX besides the OVF Templates that are provided by Check Point. - 00526862 VMware Tools are not supported on a Security Gateway VE Virtual Machine. - 00525830 To upgrade from R71 Security Gateway VE, refer to - 'Upgrading from R71 VE'. - 00566886 CPU consumption for the Security Gateway VE might show inaccurate results. To resolve this issue, reserve CPU resources on the ESX: • In the vSphere client, right click the Security Gateway VE.
- QoS - QoS does not support the following: • IPv6 • VSX - User Authority 01288683, 01289928, 01289929, 01289930 User Authority Server (UAS) does not start on 64-bit Security Gateway: [Expert@HostName]# uagstart UAS: Loading UAS driver. Mknod: missing operand after `0' Try `mknod --help' for more information. Chmod: cannot access `/dev/uag0': No such file or directory UAS: UAS driver was loaded successfully UserAuthority: Starting driver Unable to open '/dev/uag0': No such file or directory UAG module: Can't open UAG device UserAuthority: Driver load failed Refer to. Compliance Blade - Upgrade of R76 Management Server with Compliance Blade Hotfix to R77 fails with error message: • Error message on CLI: ' Pre-upgrade verification failed' • Error message in Gaia Portal: ' The file could not be retrieved' Refer to. - 00264417 Configuration of Compliance Blade is not saved after upgrade to R77. - SNMP 01289099, 01289976, 01289977, 01289978 ' Could not resolve ' Sensor' within the trap ' Trap' errors in Spectrum CA when importing Check Point ' GaiaTrapsMIB.mib' file. - SmartEvent 01313659, 01336916, 01336955, 01319013 After an upgrade, SmartEvent does not show any events and shows an error ' No connection to correlation unit'.